The rules have changed
Bad actors have moved from targeting individual companies to targeting supply chains, ecosystems, and critical infrastructure (see Arthur D. Little [ADL] Viewpoint “Developing Resilience for Global Supply Chains in Crisis”). The lines between the digital and the physical are blurring, and attackers are increasingly more patient and strategic. And, of course, AI is putting advanced tools into their hands, allowing them to move at ever higher levels of complexity.
If state actors are involved, the severity of the potential threats increases substantially, as state-sponsored groups are less driven by immediate financial gain. Instead, they are willing to invest months — or even years — in infiltrating systems and positioning themselves to inflict maximum damage at the most critical moment. And they’re not just targeting government agencies. “There are state actors working against a lot of companies, especially those in critical infrastructure,” says Maximilian Scherr, Partner in ADL’s Performance practice and co-leader of its cybersecurity function. And as global turmoil increases, so do these risks, he says.
“Cyberattacks are being used as part of warfare,” says Tom Teixeira, Partner in ADL’s Performance practice and Audit Committee Chair. Enemy actors want to create as much disruption and damage as possible, he explains.
“The real concern is serious cyberattacks on infrastructure that could lead to operational disruption and physical damage that affects citizens,” he says. “It would ultimately cost the state that’s being attacked an enormous amount in terms of finance and drain on resources.” These impacts wouldn’t necessarily be geographically limited. “The world has become more complex,” Teixeira notes. As the Jaguar Land Rover incident illustrates, an attack on one company can affect thousands of others.
There’s also increasing interconnectivity between the physical and digital worlds. Cyberattacks are no longer just about extracting data for financial gain. They can stop physical systems from operating because of the increased interdependence between IT and operational technology.
“In the transport industry, we’re having to close down airport operations,” Teixeira says. “We’ve seen that in Europe, following a cyberattack. There’s great dependency between physical hardware and the digital environment. You can’t look at a system in isolation — if one system gets taken out, multiple systems could be taken out, due to the level of interdependency and interconnectivity.”
Yet according to WEF, enterprises still aren’t taking operational technology (OT) security seriously. Only 16% of organizations with industrial environments report OT security issues to their boards, only 32% monitor OT security, and only 36% have a CISO (chief information security officer) who is responsible for both IT and OT.
That’s a mistake, says Teixeira. The CISO should oversee regular scanning for security issues in both IT and OT and be a key line of communication to the business units that own the physical systems. “The CISO also needs to be higher up in the food chain — to be able to influence senior management and the board,” he says.
Last, but by no means least, is the rise of generative AI (see ADL Viewpoint “AI in Cybersecurity”). According to WEF, 94% of leaders say AI will significantly affect cybersecurity in the next 12 months. “AI gives people who don’t have much of a clue a weapon in their hand to do harm — maybe even more harm than they think they want to do,” says Scherr. “And if you put that in the hands of people who are really smart and who do want to do harm, my God.”
"Cyberattacks are being used as part of warfare"

INVESTMENT WITHOUT PROTECTION
The core problem is that enterprises measure inputs, such as controls, policies, and certifications, instead of outputs — the ability to absorb and recover from shocks (see ADL Viewpoint “Total Cost of Risk”). It all comes down to how companies think about cybersecurity, says Robert N. Charette, an international authority on IT and risk management and a contributing editor to IEEE Spectrum. “Cybersecurity has always been viewed as an added cost,” he says. “The aftermath of an attack becomes the cost of doing business, rather than building the infrastructure they need.”
WEF examined the views of CEOs at companies with various levels of organizational resilience. Only 19% of respondents said their organization’s cyber resilience exceeds requirements; 64% said it only met minimum requirements, and 17% said it was insufficient.
According to the WEF report, the most resilient companies were also the most proactive in their approaches to cybersecurity. For example, 52% of CEOs at resilient companies prioritize threat intelligence of nation-state actors, compared to just 13% of insufficiently resilient companies.
Resilient CEOs are also eight times more likely to have increased engagement with government agencies and information-sharing groups and more than twice as likely to have increased their cybersecurity budgets. Resilient CEOs are also more focused on third-party and supply chain vulnerabilities, rapidly evolving threat landscapes, and emerging technologies.
The CEOs of non-resilient companies said their biggest challenges are a lack of skills and money. Proactive cybersecurity can be a hard sell in organizations, explains Charette. “You want me to pay you to look for things that may not happen,” he says. “Sometimes, it seems they don’t really want to know because then they would need to do something about it.”
Putting mitigation/recovery strategies in place in case an incident does occur is also a hard sell, Charette says. If the company spends the money up front, and there’s an attack, then recovery will be quicker and more efficient, so it might be less expensive over the long term — but a lot of companies prefer to pay later, he says.
Things change when a company gets attacked, says Teixeira. But only for a while. “After a cyber breach, investment takes place, and people put additional controls in place,” he says. “Then there’s this comfort that everything is under control.” But this is a false sense of security. “Cyberattacks get more sophisticated,” Teixeira notes. “Your operating model changes, and in many cases, vulnerabilities start to reappear.”
The relevant question is not whether or not an organization can prevent every attack — it’s whether it can take a severe cyber shock without suffering material damage to performance, reputation, or strategic position
FROM CONTROL MATURITY TO SHOCK TOLERANCE
This does not mean organizations need infinite budgets or perfect protection; it means they need to set a different goal. The objective is not to defend equally against every possible scenario but to understand where the business-critical vulnerabilities are, which disruptions would be existential, and how well the organization would withstand and recover from them. Here, the same forces making life harder for defenders are creating advantages. AI can help security teams do more at a lower cost, continuously testing assumptions and detecting weaknesses before adversaries can exploit them.
Michael Papadopoulos, Partner in ADL’s Innovation practice and cybersecurity co-leader, says the baseline has shifted. Organizations can use AI to go beyond detecting anomalies — scanning configurations, testing controls, analyzing source code, evaluating identity structures, and probing external exposure much faster than before. That’s significant because resilience has to be both inside-out and outside-in. It requires visibility into internal weaknesses, such as access models, unpatched systems, and weak recovery processes. It also requires an attacker’s-eye view of exposed assets, vulnerable third parties, and pathways into the organization from the outside.
Scherr says ADL’s approach to this is the Cyber Shock Tolerance Score, a structured way to assess how much disruption an organization can absorb. “We have developed a very structured methodology that goes beyond the classical NIST standards,” he says. “It’s like doing an MRI of a person from head to toe. You find stuff that you would not find if you just asked them, ‘Do you do sports? Do you eat healthy?’ If you ask, 99% of people will say they do sports and eat healthy. But when you look at the MRI, you see where the risks are. You can look at the muscle mass and see how much they exercise.”
Scherr explains that the relevant question is not whether or not an organization can prevent every attack — it’s whether it can take a severe cyber shock without suffering material damage to performance, reputation, or strategic position.
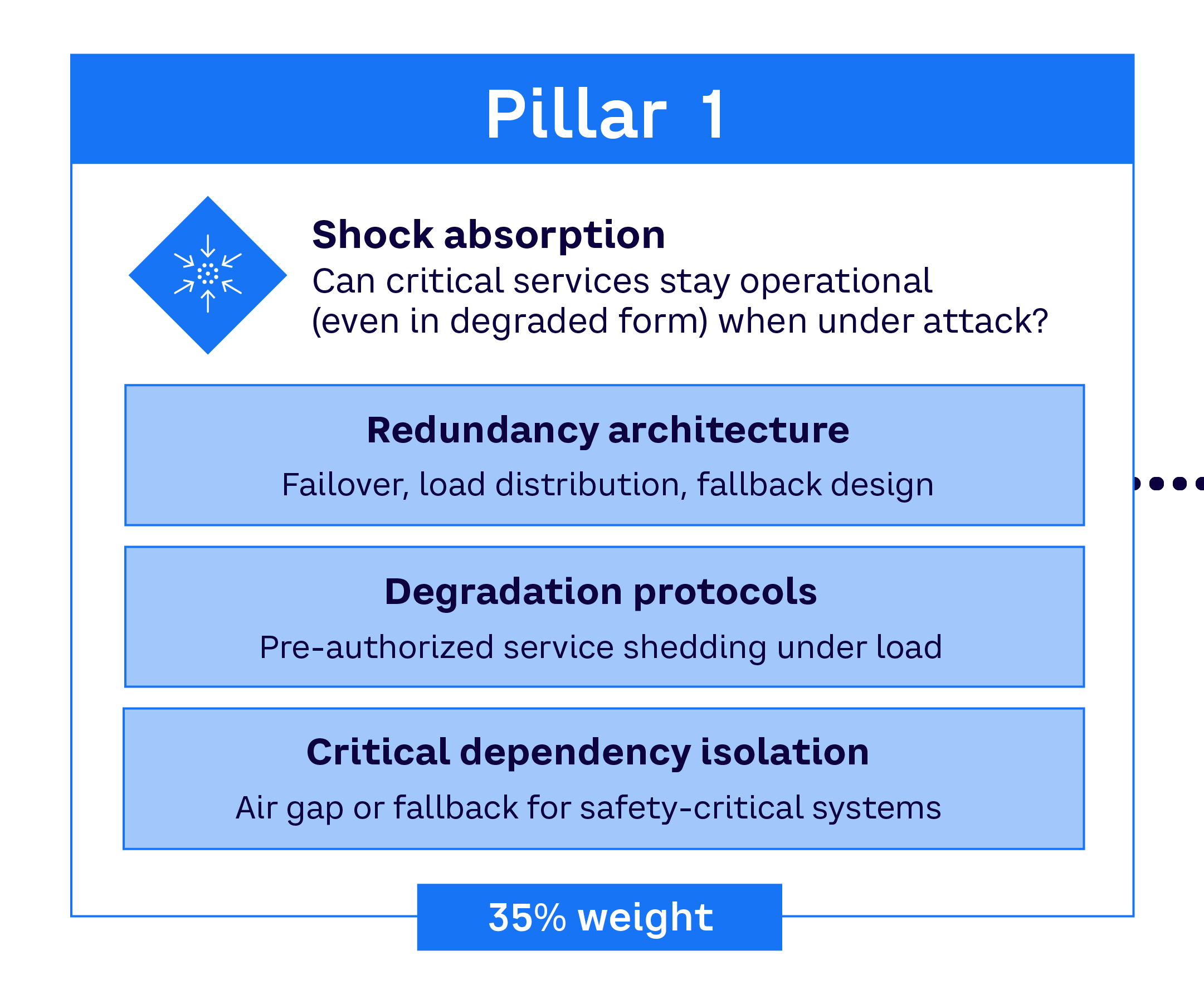
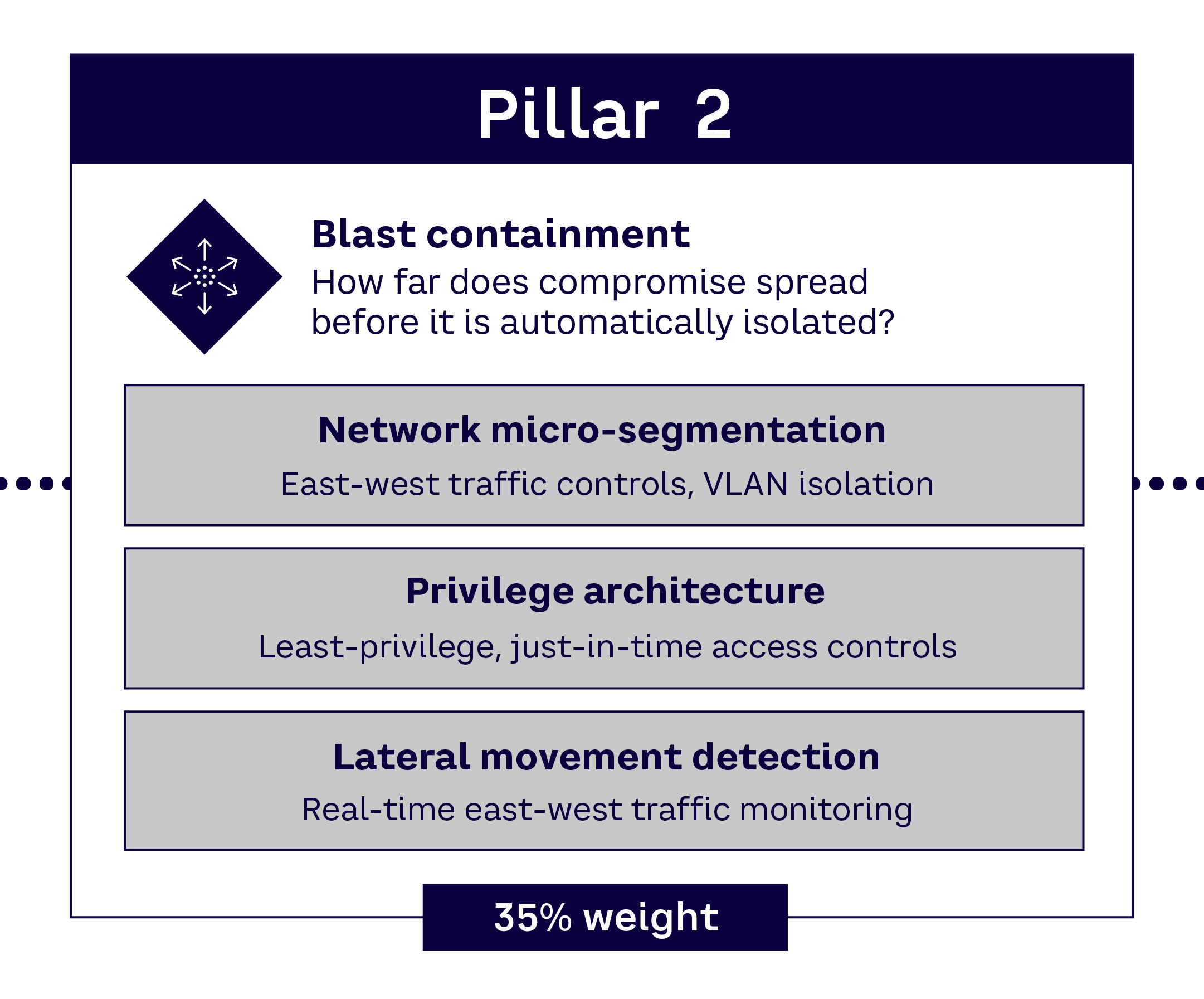
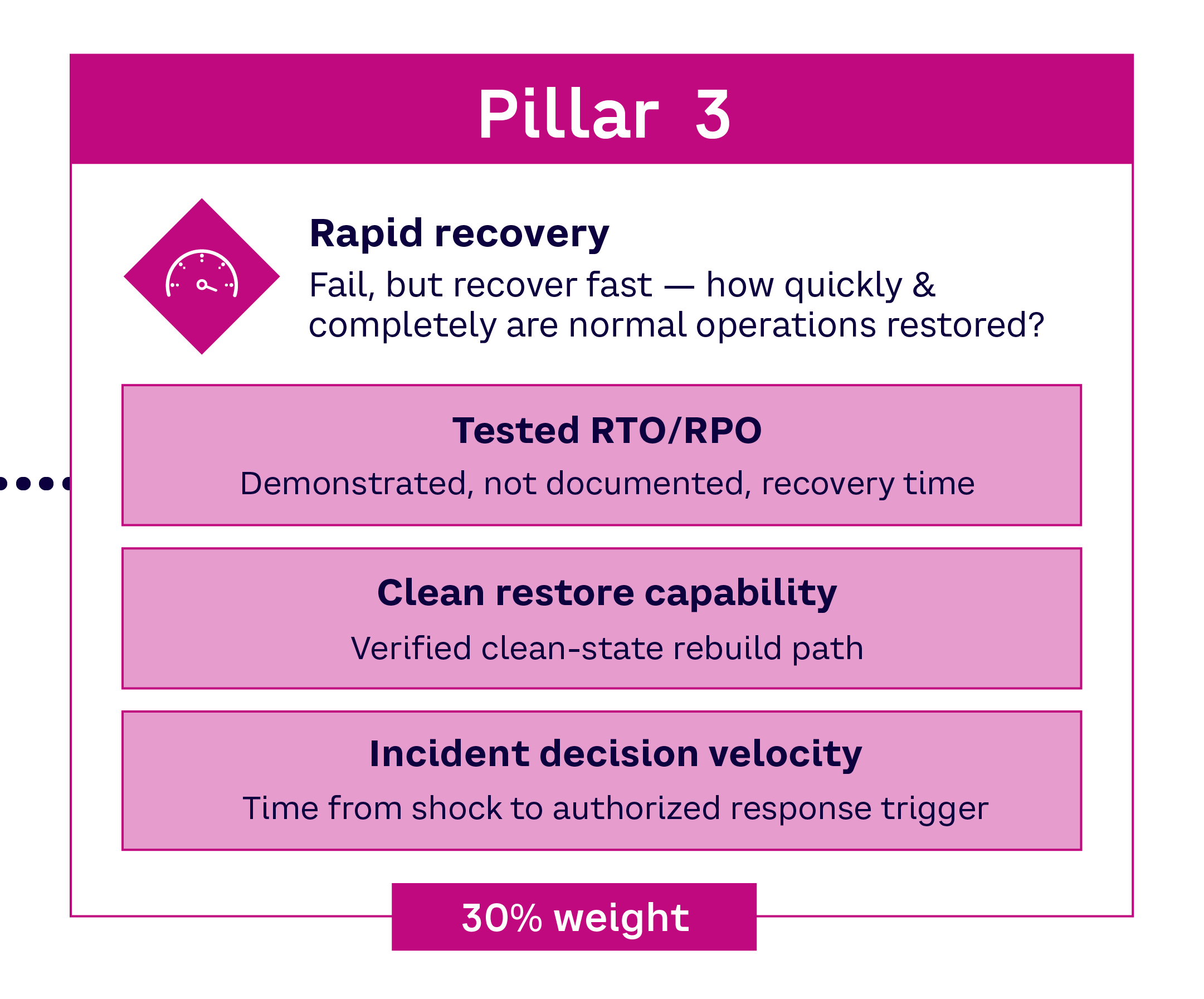
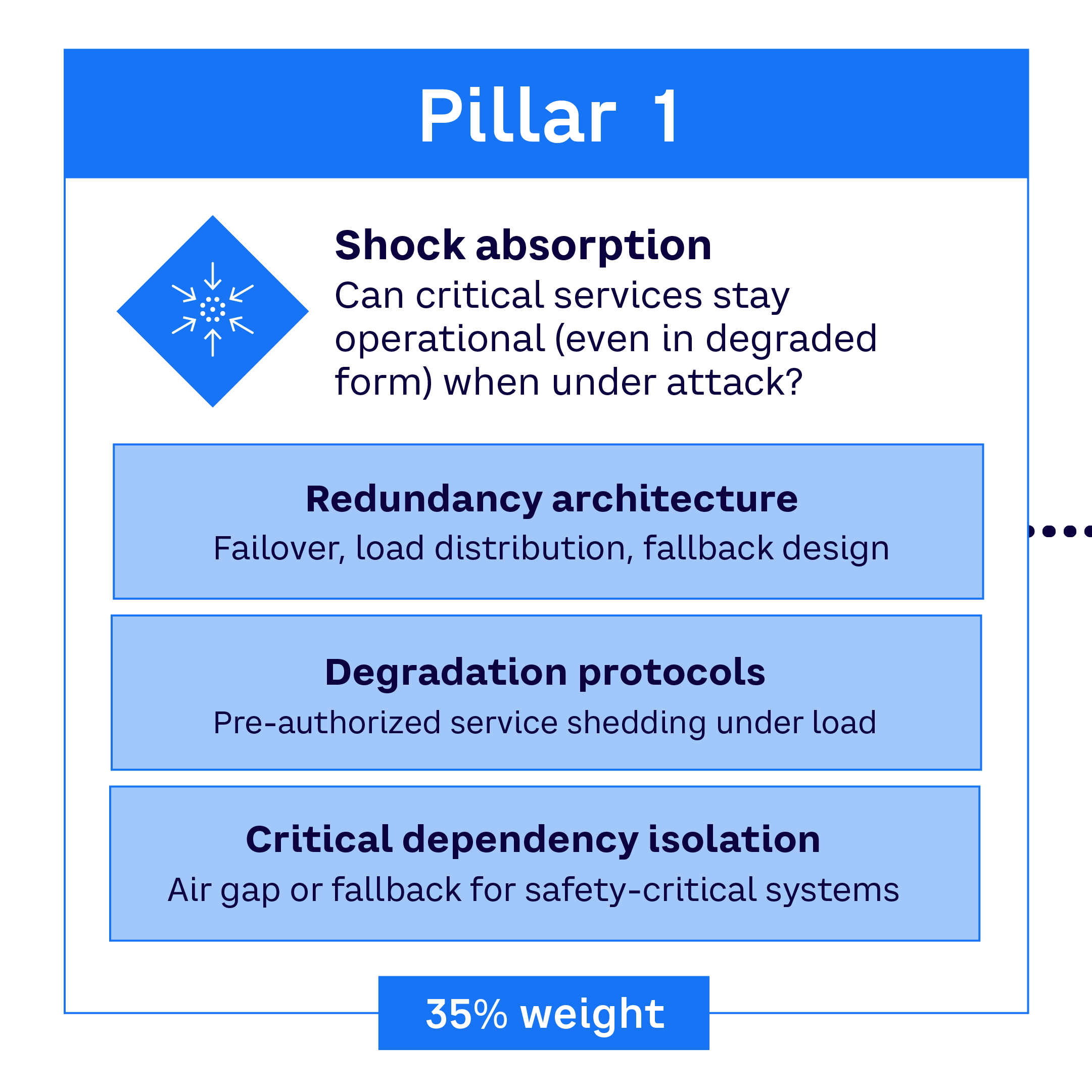
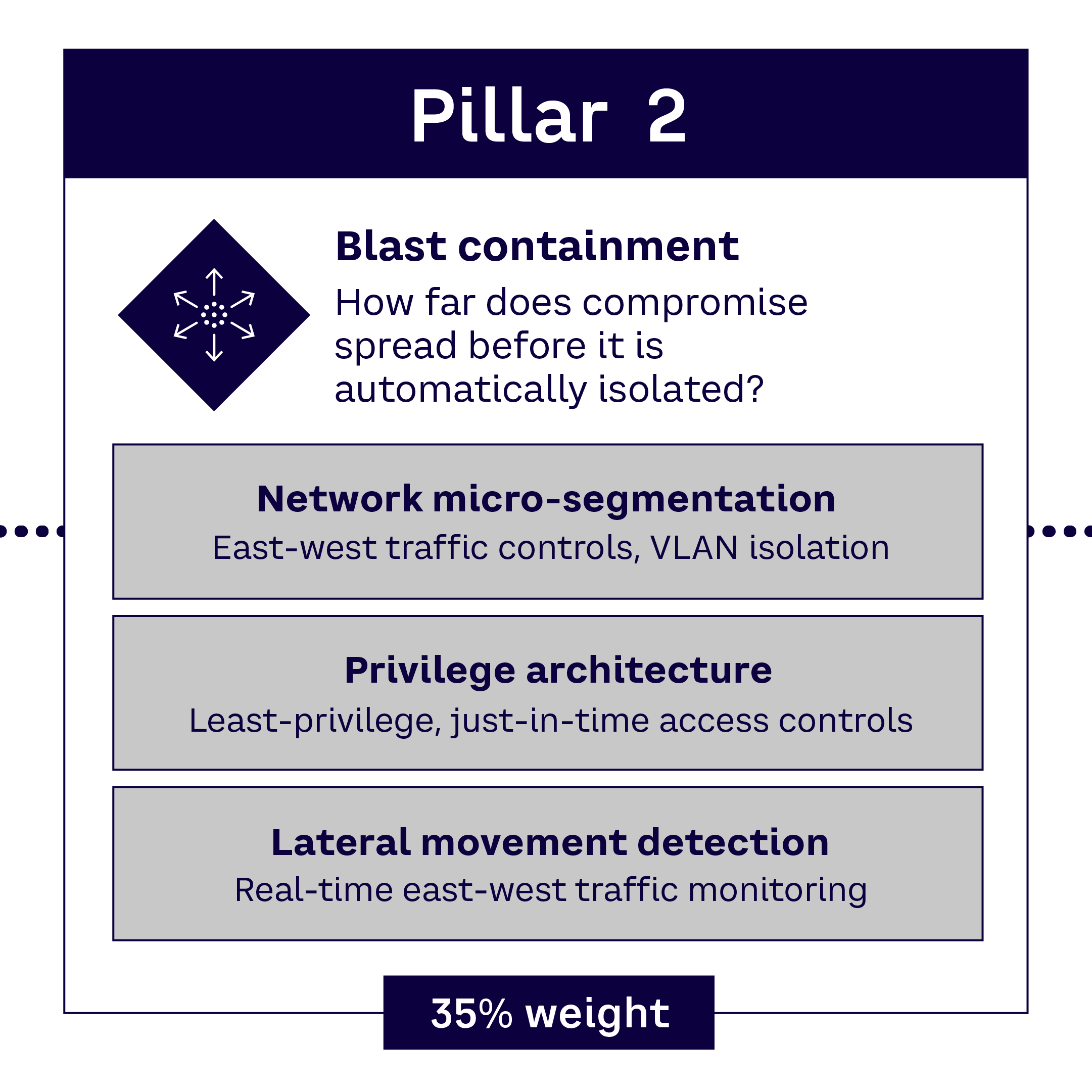
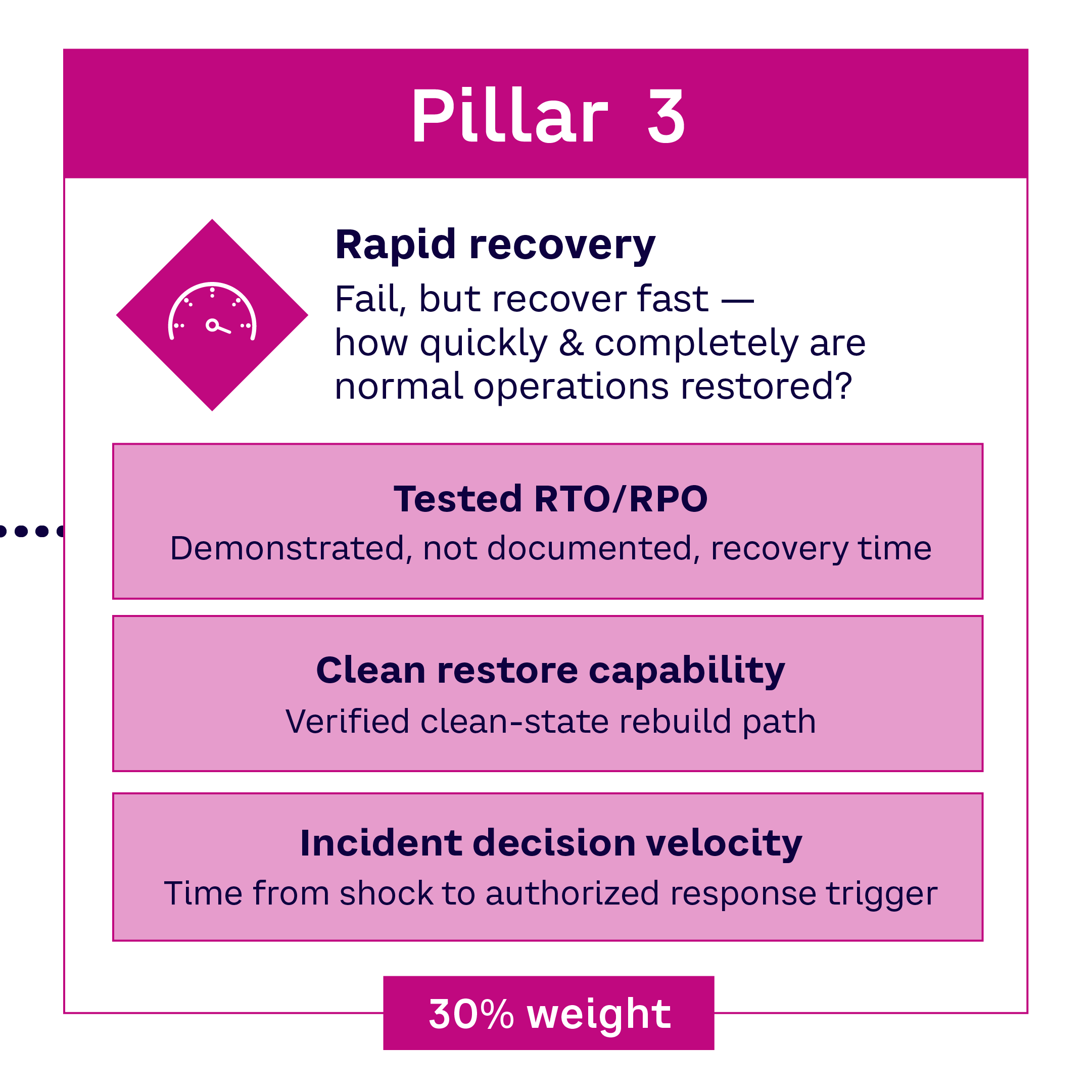
CYBER SHOCK TOLERANCE SCORE PILLARS
VLAN = virtual local area network; RTO = recovery time objective; RPO = recovery point objective; Source: Arthur D. Little
ADL weights each pillar according to its real-world importance: 35% for absorption, 35% for containment, and 30% for recovery. The result is a management view of whether the enterprise can stay within acceptable damage limits when the shock comes.
Ukrainian telecom operator Kyivstar is a good example: it has maintained critical services under wartime conditions. The company began preparing before the full-scale invasion, reserving additional communications channels, increasing network capacity, backing up databases, and moving critical equipment and warehouses to Western Ukraine. These steps allowed 93% of its base stations to remain operational after more than a month of active hostilities (shock absorption).
Kyivstar’s engineers were able to remotely switch traffic away from damaged network segments, limiting the impact of local destruction while highlighting the European points of presence in Warsaw, Amsterdam, and Frankfurt (blast containment).
The company’s response to the December 2023 cyberattack was equally telling: partial fixed-line services were restored the same day, and within a week, Kyivstar reported that all service categories had been restored, with 99% of base stations in government-controlled territory back on-air (rapid recovery).
Obviously, the company could not avoid these external shocks, but it clearly demonstrated what companies can do to absorb, contain, and recover under extreme stress.
CYBER SHOCK TOLERANCE SCORE PROFILES
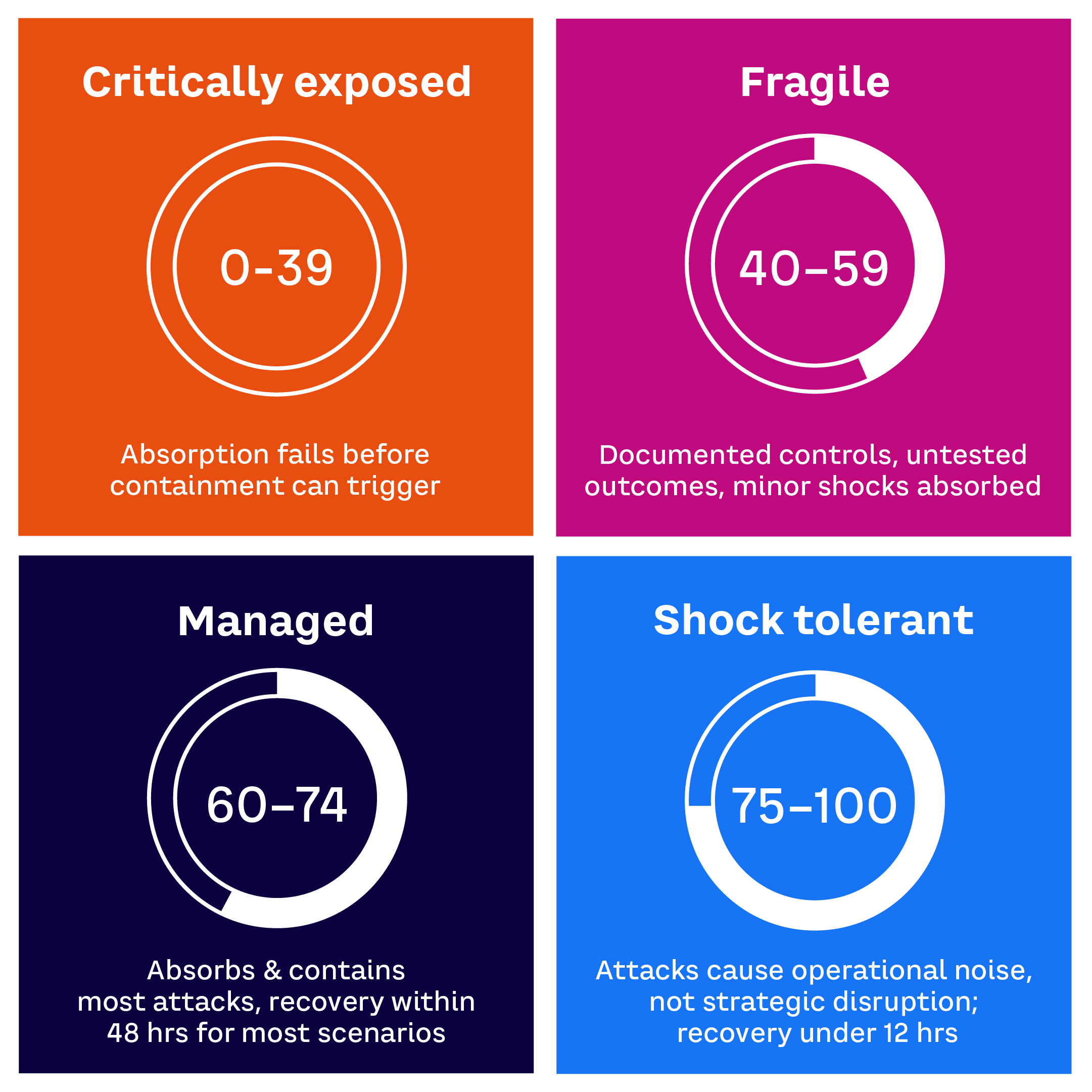
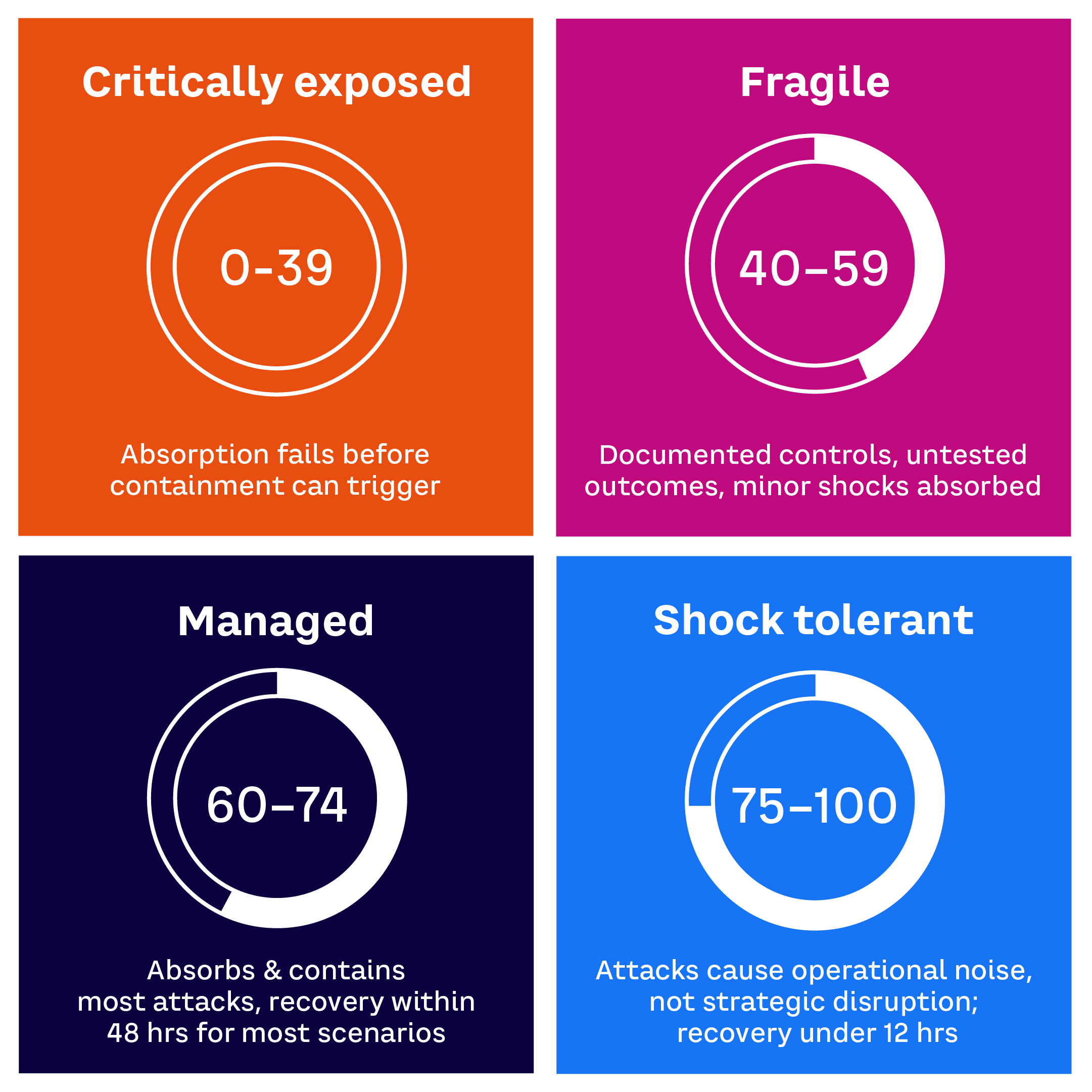
Source: Arthur D. Little
Importantly, ADL’s Cyber Shock Tolerance Score is linked to its Cybersecurity Matrix (see ADL Viewpoint “Being Concerned Is Not Enough”). The matrix assesses cybersecurity across six domains and six functional areas, and the Cyber Shock Tolerance Score adds a new lens. It expands the analysis into whether those controls enable the organization to (1) absorb disruption, (2) contain the blast radius, and (3) recover operations under real stress. Essentially, the 6×6 matrix shows the maturity of the control environment, while the Cyber Shock Tolerance Score shows the implications of the current controls for the business under pressure.
CYBERSECURITY MATRIX
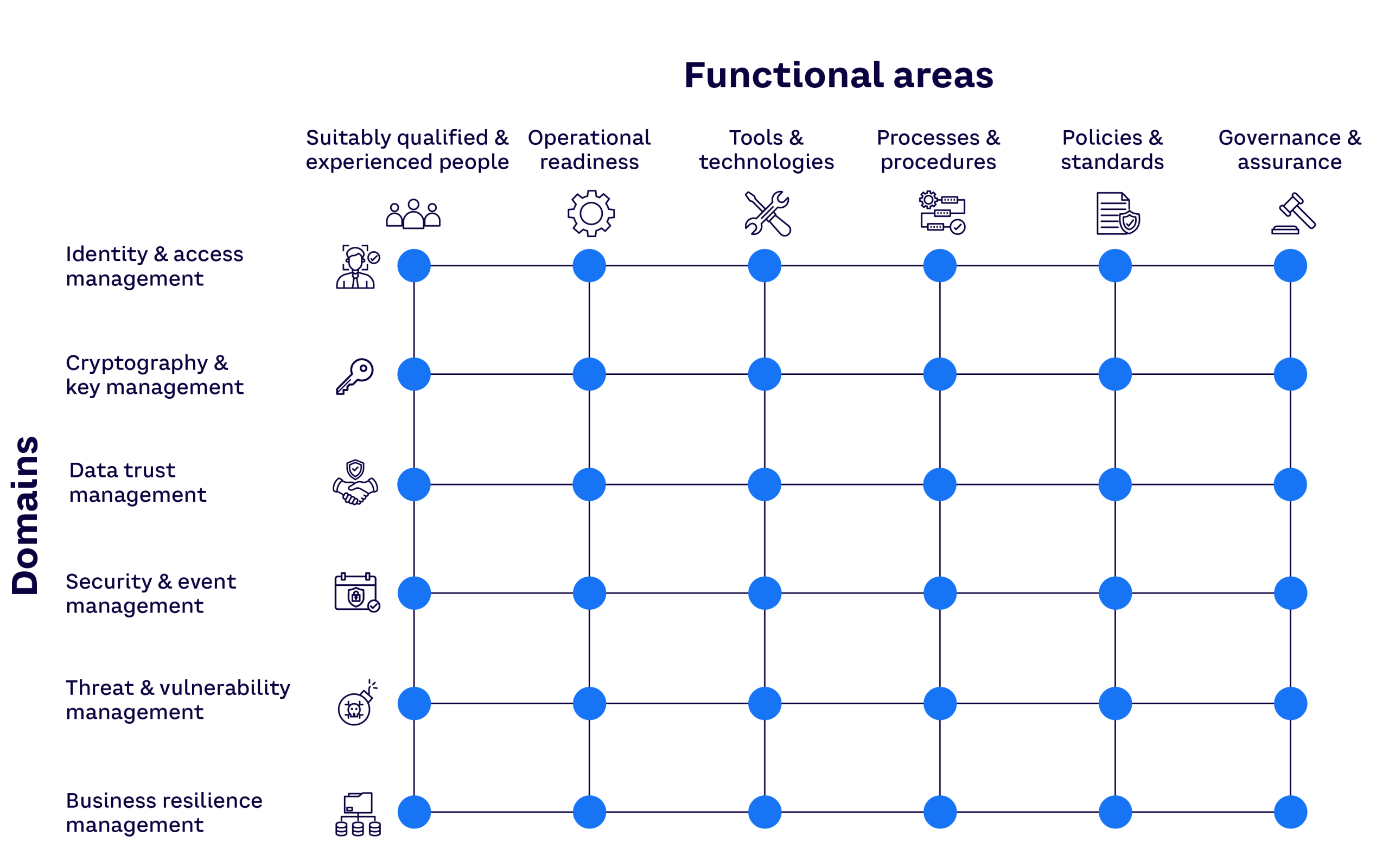
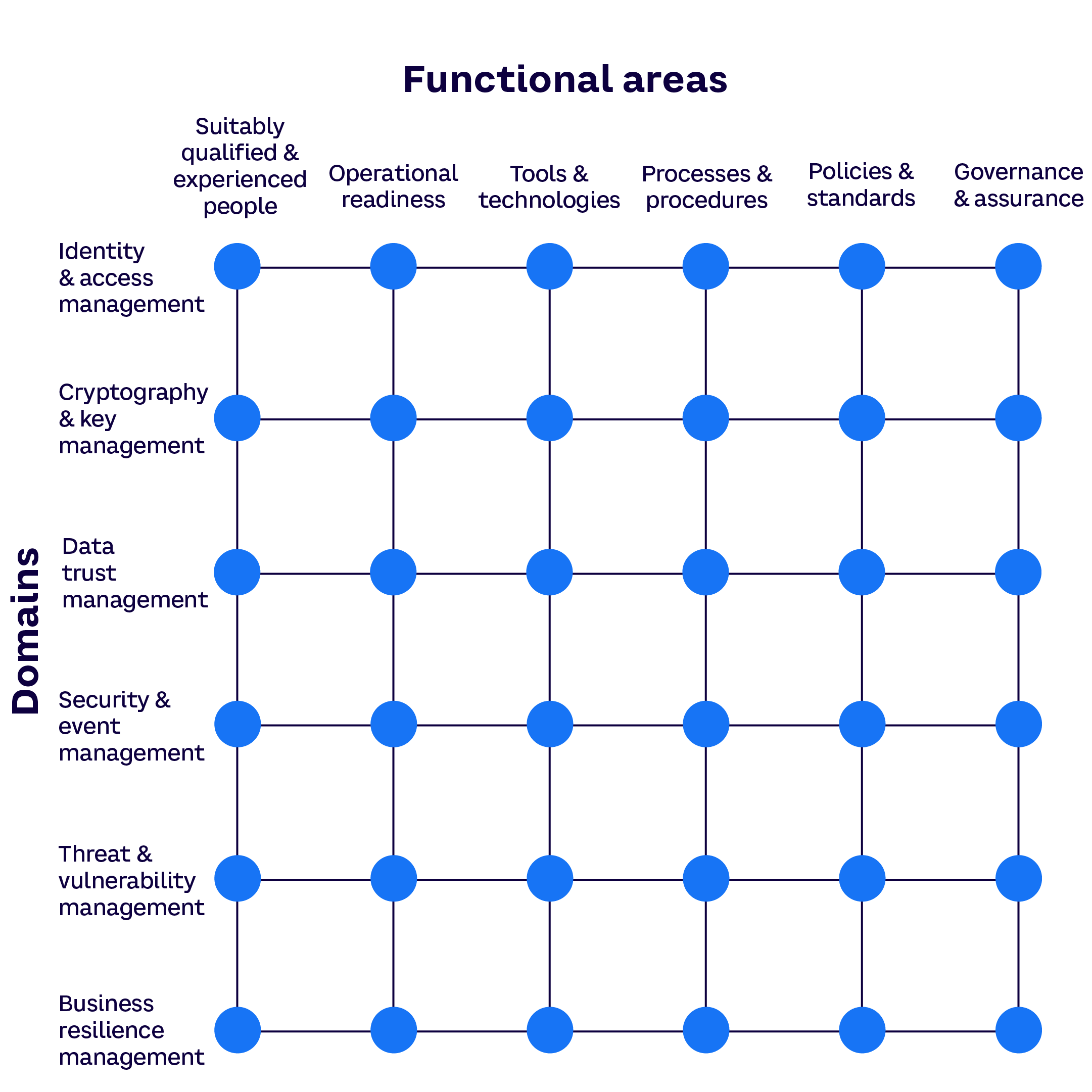
Source: Arthur D. Little
This addition matters because under severe conditions, one weak pillar can act as a sequential multiplier: absorption fails before containment can trigger, or recovery takes weeks rather than days because the restore path was never truly tested. The Cyber Shock Tolerance framework is designed to make that visible.
This approach also helps expand the board conversation into whether the business can keep operating, contain the event, and restore trust before the damage becomes material. Many companies can describe their control environment in reassuring terms; far fewer can demonstrate evidence as to what would happen under real stress.
WHAT LEADERS MUST DO
Security starts in the boardroom, not the server room, says Scherr. “If it’s not a priority for the board, then it doesn’t get the budget, the people, or the attention it needs.”
Boards do not need to become technical experts, but they do need to ask better questions. What must never go down? Which dependencies could create systemic failure? How exposed are we through suppliers, partners, and OT environments? How long would recovery take? What would the financial, operational, and reputational impact be if a major shock hit tomorrow?
The most effective way to focus leadership attention is to translate cyber risk into business impact. “The only time you get senior management attention focused on building resilience is when you can put a physical number on it,” says Teixeira.
Fortunately, AI makes it far easier to simulate the impact of emerging threats. “You can model this, and then, with a certain level of confidence, you can understand what the financial impact is going to be,” he says. “In the past, we’ve found that many chief risk officers didn’t have a strong enough voice until they could show potential impacts, such as how much it could hurt earnings or negatively affect financial KPIs. Then we see management start to pay attention.”
That shift in language is essential. Cybersecurity framed as technical hygiene struggles to win the funding competition. Cyber resilience framed as earnings protection, continuity assurance, and trust preservation commands attention.
The next major cyber event may not look like a breach. It may look like an operational shutdown, a supply chain cascade, or a loss of trust that spreads faster than the incident itself

BREACHES ARE SO 1990s
Companies that will outperform in this threat environment are not those with the longest list of controls or the most polished compliance dashboards. Rather, they understand their vulnerabilities, continuously test assumptions, rehearse recovery under pressure, and treat cyber resilience as a core business capability rather than an IT program.
The next major cyber event may not look like a breach. It may look like an operational shutdown, a supply chain cascade, or a loss of trust that spreads faster than the incident itself. For many organizations, the question is no longer whether they are secure enough — it’s whether they are one shock away from an incident from which they cannot recover.
KEY TAKEAWAYS
- Cyber risk has moved beyond financial crime into geopolitical competition, operational disruption, and systemic shock.
- Many organizations still measure cyber maturity through controls and compliance rather than their ability to absorb, contain, and recover from disruption.
- Governance failures are as dangerous as technology gaps, and the CISO needs a genuine seat at the table.
- Resilience is not a certification moment. It requires continuous scanning, tested recovery, and a culture that treats complacency as a substantial risk.